Tella Licensing
Licensing platform with encrypted FiveM validation, Stripe-powered checkout, and a self-serve portal where developers keep 100% of their product revenue.
Context
Tella Licensing was built to solve a recurring problem in the FiveM ecosystem: developers were spending too much time manually creating, sending, rotating, and revoking license keys while users had a fragmented purchase and activation experience.
The project scope was a 2-3 week implementation sprint that included product strategy, UI/UX design, API architecture, checkout integration, and script-side validation flow for protected resources.
Problem
The legacy workflow created failure on both sides of the marketplace:
- Developers handled licensing through DMs and ad hoc spreadsheets.
- Customers had no single place to view products, retrieve keys, or manage activations.
- Paid resources were frequently redistributed without authorization.
- Support channels absorbed repetitive key-reset and setup questions.
The core product need was a secure, low-friction licensing layer that worked for both buyer and seller workflows.
Users
- FiveM developers selling scripts and resources.
- Server owners purchasing and activating paid resources.
- Community staff handling support and entitlement disputes.
Product Goals
- Replace manual key handling with automated provisioning.
- Provide a unified portal for key and product ownership management.
- Let developers run their own store and receive payments directly.
- Protect runtime resource access with encrypted API-backed checks.
- Build a sustainable platform model with subscription revenue and no sales commission.
Business Model
The platform model is intentionally developer-aligned:
- Developers connect and use their own Stripe credentials for store payments.
- Product revenue goes directly to the developer’s Stripe account.
- Tella Licensing takes no commission on product sales.
- Platform revenue comes from a recurring monthly subscription.
This creates clear incentives: developers keep the full cut from each sale while paying predictable platform fees for tooling and infrastructure.
UX Strategy
The UX direction focused on reducing operational friction while increasing confidence at each high-risk touchpoint.
- Minimize cognitive load in onboarding and key activation.
- Surface ownership and entitlement status without requiring support contact.
- Separate user and developer concerns without duplicating complexity.
- Keep high-risk actions explicit, reversible, and auditable.
Solution Overview
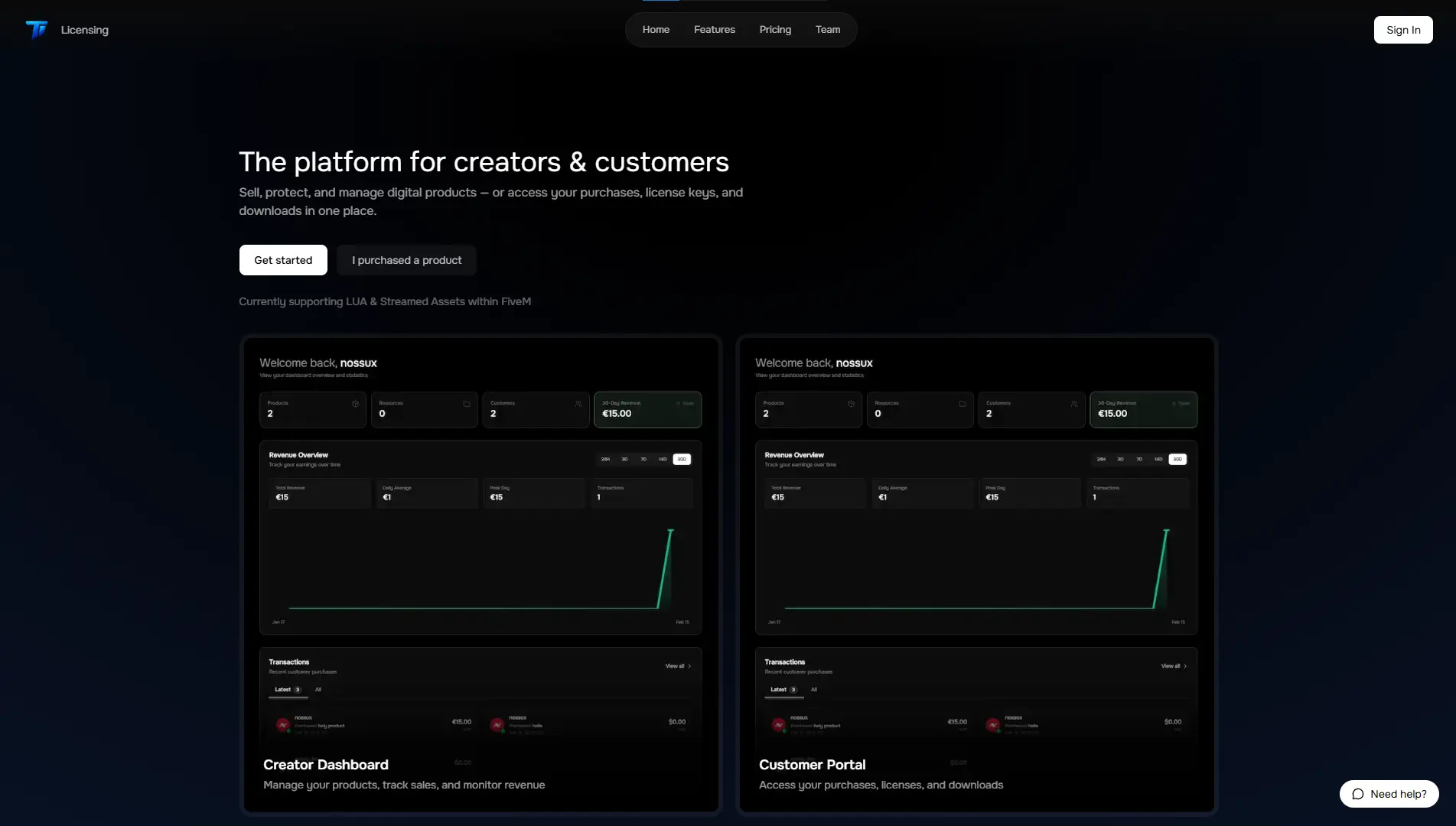
The delivered system combined four product surfaces:
- Landing page that communicates trust, value, and setup flow.
- Customer portal to manage owned products, license keys, and activations.
- Developer dashboard to publish products and operate a Stripe-backed store.
- Validation API consumed by FiveM scripts to authorize resource usage at runtime.
Landing Page
The landing page was designed as a conversion-first entry point with a clear hierarchy:
- Primary CTA to start using the portal or visit the store.
- Secondary trust blocks explaining security, ownership, and entitlement flow.
- Process framing that explains purchase to activation in a short sequence.
The result was lower ambiguity for first-time visitors and a faster path into account creation and purchase flow.
Portal Experience
The portal centralizes account and product lifecycle actions:
- View all owned products in one dashboard.
- Access and rotate license keys.
- Bind and review allowed hardware and network identifiers.
- Track active and invalidated activations.
- Recover access without admin intervention.
This shifted the support burden from manual staff handling to user self-service.
Payment Integration
Stripe integration was implemented to support direct developer payouts and platform independence from transaction commissions:
- Checkout is initiated from developer storefront product pages.
- Successful payments trigger entitlement creation and key issuance.
- Entitlements are synchronized to the customer portal immediately after payment confirmation.
- Billing for platform access is handled through recurring subscription plans.
Operationally, this separates platform billing from product sales while preserving a clean purchase experience for end users.
FiveM Script Integration
Protected resources call the licensing API from the FiveM side before enabling runtime behavior.
High-level flow:
- Resource boot process sends license payload to the validation endpoint.
- API checks license state, ownership, HWID, and source IP policy.
- API returns an encrypted authorization result.
- Script decrypts and verifies response before unlocking resource execution.
If validation fails, the resource remains locked and emits actionable error states for diagnostics.
Security Model
Security design was built around layered checks, not a single gate:
- License key validation tied to owned entitlements.
- HWID and IP binding policies for anti-sharing enforcement.
- Encrypted request and response handling between script and API.
- Key lifecycle controls: issue, rotate, revoke, and expire.
- Auditable event logging for activation and validation actions.
This model reduced unauthorized reuse while maintaining manageable recovery paths for legitimate users.
Technical Architecture
- Frontend: Next.js and Tailwind for fast iteration and consistent UI system.
- Components: Headless UI for accessible interaction primitives.
- Data layer: Prisma-backed relational modeling for users, products, keys, and entitlements.
- Payments: Stripe for checkout and subscription billing.
- Runtime integration: FiveM resource callbacks to licensing API.
Architecture decisions prioritized maintainability and operational clarity over premature complexity.
Validation
Validation was run across product, support, and runtime dimensions:
- Tested purchase-to-entitlement consistency through Stripe webhook paths.
- Simulated invalid and replayed license payloads for failure handling.
- Verified locked behavior in FiveM resources when checks fail.
- Reviewed support channel volume after self-service rollout.
Outcome
- Licensing operations moved from manual handling to automated workflows.
- End users gained a clear path for purchasing, activating, and managing products.
- Developers gained direct payment ownership and kept 100% of product revenue.
- Platform sustainability was established through recurring subscription fees instead of transaction cuts.
Lessons Learned
- Developer trust improves when payment ownership is explicit and commission-free.
- Runtime protection works best when paired with strong recovery and audit tooling.
- Entitlement UX is as important as encryption in reducing support burden.
Next Iteration
- Add anomaly scoring for suspicious activation patterns.
- Expand policy controls for per-product security profiles.
- Introduce richer analytics for conversion, churn, and key lifecycle health.